Secure Your Organisation with
Leading Cybersecurity
Solutions
Protect, Evolve, and Innovate with
Itec’s Advanced Cybersecurity Solutions

Seamlessly Integrate into Your Network
Safeguard Against
Threats
Protect Your
Devices
Advanced Threat
Detection
Managed Detection & Response (MDR)
Our MDR service provides 24/7 human-led threat detection and response, backed by breach warranty protection. Key features:
- Continuous monitoring by security analysts.
- Threat hunting and incident triage.
- Rapid containment and remediation support.

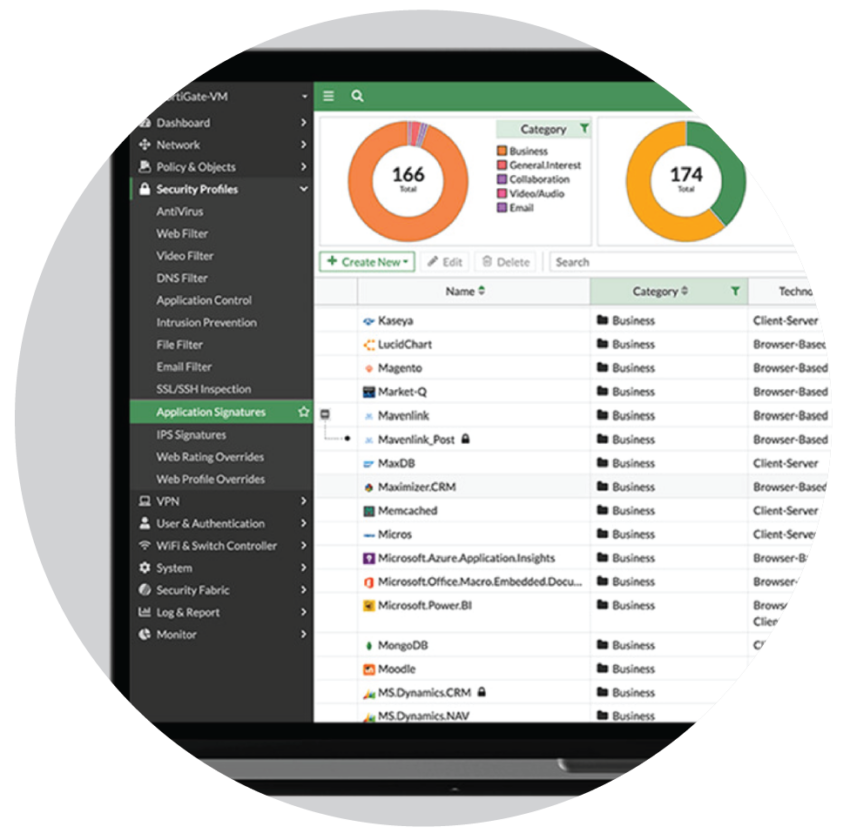
Managed Firewalls
We configure and manage firewalls according to industry best practices to ensure optimal protection and performance. This includes:
- Policy tuning and rule optimisation.
- Threat prevention updates.
- Proactive oversight and incident response integration.
SASE
Secure Access Services Edge, more commonly known as SASE, is the next iteration of cybersecurity in the cloud. Chances are, you’re already leveraging some elements of SASE, such as Zero Trust or a Software -Defined Wide Area Network (SD-WAN) in your environment.
- Cloud-first Approach to Architectural Framework.
- Comprehensive, Simplified Security.
- Optimised Performance and User Experience.


Endpoint Protection & XDR
We deliver cutting-edge endpoint security solutions designed to protect your business from evolving cyber threats. By integrating Extended Detection and Response (XDR) capabilities, our platform goes beyond traditional antivirus to provide holistic protection across endpoints, networks, and cloud workloads. Our solution empowers your security team with:
- AI-Driven Threat Detection.
- Real-Time Response and Containment.
- Centralised Visibility and Analytics.
Email & DMARC Protection
Tailored to seamlessly fit into your communication channels, our solution safeguards against threats while enhancing the integrity of your emails, securing your email domain against spoofing and phishing by implementing DMARC, SPF, and DKIM protocols. Key benefits:
- Improved email deliverability.
- Protection against impersonation.
- Visibility into unauthorised email usage.


Vulnerability Assessments & Penetration Testing
We identify and assess potential weaknesses in your environment through controlled simulation of real-world attack techniques. Our service includes:
- Detailed reporting of vulnerabilities.
- Remediation guidance.
- Alignment with governance, risk, and compliance (GRC) frameworks such as ISO 27001, NIST, and POPIA.
Governance & Compliance
We ensure that every solution we deliver aligns with industry best practices and your organisation’s unique governance and compliance frameworks. Our services include:
- Risk Assessment & Gap Analysis.
- Policy Development & Alignment.
- Continuous Compliance Monitoring.
- Regulatory Readiness.

Secure every process, project every insight
Fill out the form below, and a Product/Solution specialist will reach out to you.